Searches for “thejavasea.me leaks aio-tlp370” usually indicate interest in a leak bundle circulating online. The phrase combines what appears to be a file-sharing or leak site name with an “AIO” (All-In-One) tool package identifier. Before clicking anything connected to that keyword, it is important to understand what this terminology typically means and what risks are involved.
This guide focuses strictly on clarity, legality, and security. It does not explain how to obtain or access any leaked material.
What “thejavasea.me leaks aio-tlp370” Likely Means
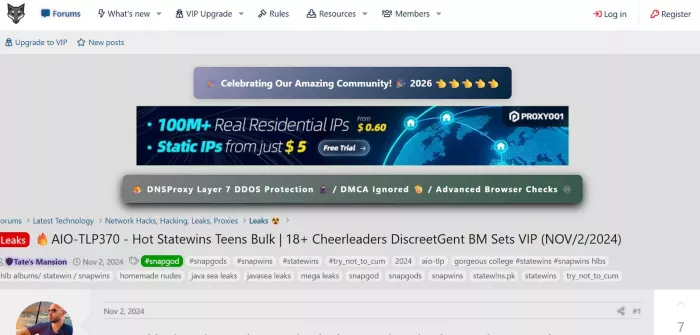
The term appears structured like many leak-related keywords used in underground communities. It likely refers to:
1. thejavasea.me — a site name referenced in discussions about shared files or leaked content
2. leaks — unauthorized distribution of software, media, databases, or digital tools
3. AIO — shorthand for “All-In-One,” meaning a bundled collection
4. TLP370 — likely a version number or release identifier
In online leak ecosystems, an “AIO-TLP” package often claims to contain a large bundle of tools, scripts, cracked software, or restricted-access resources. The number appended to it typically signals a release iteration.
It is crucial to separate the two concepts:
● Legitimate software toolsets distributed by official developers
● Unauthorized leak bundles were redistributed without permission
The second category frequently violates copyright laws and carries a significantly higher security risk.
Why People Search for This Keyword
The search intent behind this phrase is rarely random. Most users fall into one of several motivations:
1. Curiosity about what the bundle contains
2. Attempt to access paid tools without paying
3. Interest in hacking or tech-mod communities
4. Looking for “free alternatives” to licensed software
5. Social media influence or forum discussions
Many users mistakenly believe leak bundles are simply “free versions” of legitimate software. In reality, they are often modified packages whose contents cannot be verified.
Another common misconception is that downloading is legally harmless if you are not the uploader. In many jurisdictions, this is incorrect. Unauthorized downloading of copyrighted content can still expose individuals to liability.
How Leak Bundles Like AIO-TLP370 Are Typically Distributed
Leak packages are rarely distributed through transparent or traceable channels. They commonly appear via:
1. Torrent files
2. Password-protected ZIP or RAR archives
3. Cloud storage links
4. File-hosting mirrors
5. Encrypted download containers
6. Private messaging groups
These packages often include multiple subfolders with executables, scripts, patchers, and “keygen” files. Password protection is frequently used to prevent automated scanning by antivirus software before extraction.
Because these bundles are assembled by unknown individuals, there is no guarantee that the contents match the advertised description.
What AIO-TLP370 Might Claim vs What It Often Contains
Leak bundles labeled as “AIO” (All-In-One) are usually marketed as high-value packages that combine multiple premium resources into a single download. They often claim to include premium software suites, automation tools, hacking utilities, streaming bypass programs, game modification tools, or paid productivity applications. The appeal is convenience and perceived value — one archive that supposedly gives access to everything.
The marketing around these bundles typically emphasizes exclusivity and cost savings. By presenting the package as a numbered release such as “TLP370,” it may appear organized, updated, or professionally assembled. This structure can create the impression that the bundle is maintained and reliable, even though its origins are usually anonymous.
In reality, these packages frequently contain modified executables rather than clean versions of the advertised tools. Installers may be altered to include hidden background processes, and some files may run silently when extracted or executed. Instead of fully functional premium software, users often encounter outdated, partially working, or entirely nonfunctional tools.
More concerning is the common inclusion of malware embedded inside installers or key generators. Credential-stealing scripts, spyware, or remote-access components can be disguised as patchers or activation files. Because the bundle is large and contains many files, users may not notice unfamiliar components running in the background.
The fundamental issue with “all-in-one” leak bundles is scale. The larger the archive, the harder it becomes to verify what each file does. Combining unrelated tools into a single compressed package increases risk because it expands the attack surface. Even if one file appears legitimate, another file within the same bundle may be malicious.
Security Risks: Why Leak Downloads Are High-Risk
Leak-related downloads are among the most common malware distribution methods. Attackers know users searching for “cracks” or “leaks” are more willing to:
1. Disable antivirus software
2. Run unknown executables as administrator
3. Ignore security warnings
Common threats found in leak bundles include:
1. Keyloggers
2. Credential stealers
3. Crypto miners
4. Ransomware
5. Remote access trojans (RATs)
6. Backdoors
Once installed, these threats can:
1. Capture login credentials
2. Monitor keystrokes
3. Encrypt personal files
4. Provide remote control access
5. Spread to other systems
Many ransomware cases begin with pirated or leaked software downloads.
Risk Comparison Overview
| Risk Type | What It Involves | Potential Impact |
| Legal Risk | Copyright infringement | Fines, legal action |
| Security Risk | Malware infection | Data theft, ransomware |
| Ethical Impact | Unauthorized redistribution | Financial harm to creators |
Data Privacy Concerns
Leak bundles sometimes include more than just cracked tools. In some cases, they contain stolen databases, exposed credentials, or bundled scripts designed to harvest personal data.
If a malicious file runs on your system, it may:
1. Capture stored browser passwords
2. Access email accounts
3. Extract cryptocurrency wallet data
4. Transmit files to remote servers
Because leak bundles are anonymous, tracing accountability is nearly impossible.
Tool vs Malware Indicators
| Indicator | Lower-Risk Legitimate Tool | Higher-Risk Leak File | Why This Matters |
| Official website presence | Hosted on a verifiable, professional domain with contact details and company information. | Shared through anonymous forums, file-hosting links, or mirror sites with no clear ownership. | Legitimate developers maintain traceable websites. Anonymous distribution removes accountability and increases fraud risk. |
| Digital signature | Signed with a verified publisher certificate that your operating system can validate. | No digital signature or shows an unknown/untrusted publisher warning. | Digital signatures confirm file authenticity. Missing or invalid signatures are common in tampered or malicious files. |
| Transparent documentation | Includes clear installation guides, version notes, changelogs, and support references. | Instructions are vague, minimal, or encourage ignoring security warnings. | Professional documentation reflects legitimate development. Poor or suspicious instructions often signal manipulation. |
| Requires disabling antivirus | Does not require disabling security tools to function properly. | Frequently instructs users to turn off antivirus or firewall before running. | Malware often triggers antivirus alerts. Asking users to disable protection is a major red flag. |
| Distribution channel | Downloaded from official stores, developer sites, or verified repositories. | Distributed via torrents, encrypted archives, or anonymous links. | Trusted platforms vet files. Anonymous channels allow malicious code to spread unchecked. |
| File structure clarity | Contains only necessary installation files relevant to the tool. | Large bundles with unrelated executables, scripts, and hidden background files. | Excess files increase attack surface and make it harder to identify malicious components. |
| Permission requests | Requests only necessary permissions for functionality. | Asks for administrative access without clear justification. | Excessive permission requests can enable system-level compromise. |
If a file requires you to disable security protections, treat it as high risk.
FAQ Based on Real Search Intent
Is thejavasea.me leaks aio-tlp370 safe?
There is no verifiable evidence suggesting safety. Leak bundles distributed anonymously present a high malware risk.
Is downloading leaked files illegal?
In many jurisdictions, yes. Downloading unauthorized copyrighted material can violate the law.
Can these leaks harm my device?
Yes. Leak bundles frequently contain malware capable of stealing credentials or encrypting files.
Why do people share leaked tool bundles?
Motivations vary: attention in underground communities, ideological piracy beliefs, monetizing traffic, or intentionally spreading malware.
Final Perspective
The keyword “thejavasea.me leaks aio-tlp370” appears connected to a leak-style bundled tool package. While it may be marketed as an all-in-one resource, such bundles carry:
1. Significant security risk
2. Potential legal exposure
3. Ethical concerns
4. High probability of malware infection
If the content is described as a “leak,” especially as an “all-in-one package,” assume elevated risk.
The safest approach is simple: obtain software only from official, verified sources. The cost of legitimate access is almost always lower than the cost of device compromise, identity theft, or legal trouble.




Comments